Nano-enabled Hardware Security
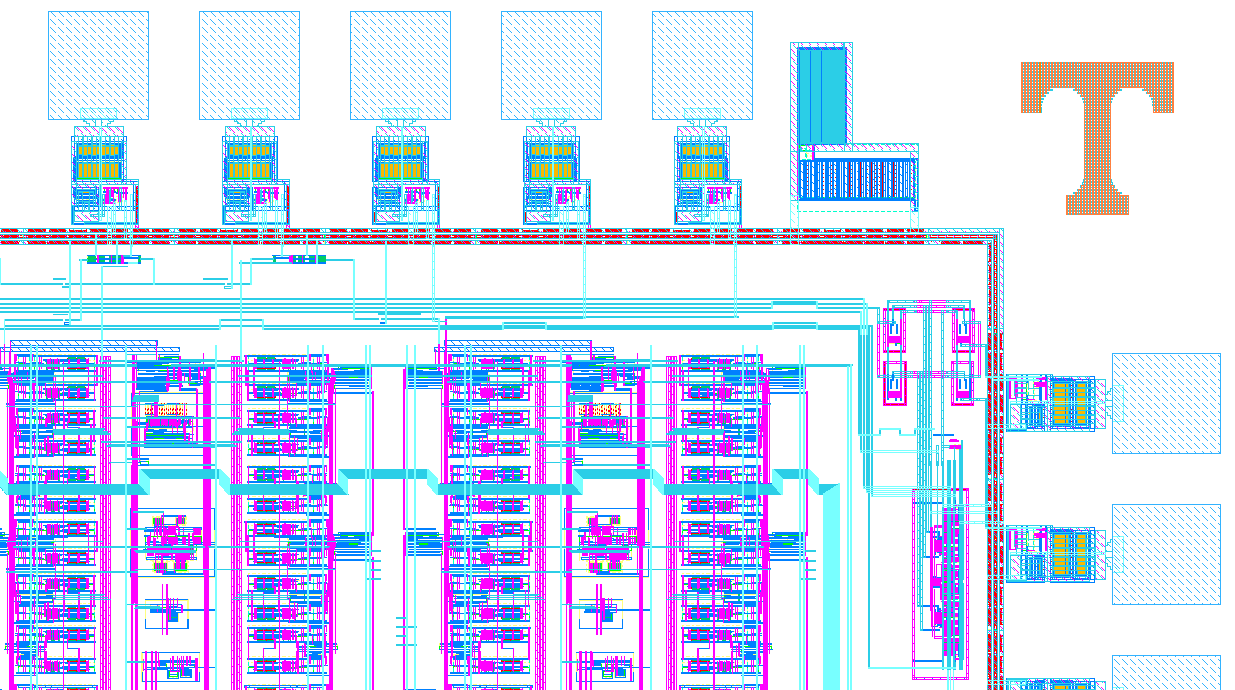
As is the case with any modern computing system, nanoelectronic architectures must be designed and implemented with special attention paid to potential security concerns. For example, a hardware encryption engine can be designed to provide high security encryption but if not implemented properly information leakage via side-channels (e.g. power) can be exploited by malicious parties to retrieve sensitive information. Side-channel attacks have emerged as a serious concern for computer systems and even strong encryption techniques such as AES can be susceptible to leaky side-channels if the overall system is not designed properly. Recent work in this area includes the design and simulation of a memristor-based system that minimizes the likelihood of a side-channel attack by leveraging the reconfigurability and inherent process variations of memristors.
Hardware security is also concerned with issues such as counterfeiting and design piracy where malicious parties could enter the supply chain for integrated circuits. One popular solution explored by many research groups for combating hardware security concerns is the use of a physical unclonable function (PUF) that can provide unique "fingerprints" for integrated circuits or be used to generate secret keys. A PUF leverages the inherent process variations of an integrated circuit (typically bad news) to generate digital responses that are unique to a particular device implementation. Nanoelectronic PUF circuits have been designed that leverage process variations in properties such as the write-time of memristive devices. More specifically, when driving a write pulse across several memristors simultaneously we have shown that some of the devices will switch and some will not. A unique PUF response can then be generated based on which memristive devices switch. The construction of hardware security primitives from nanoscale devices such as memristors is expected to lead to secure hardware with a small footprint and low power consumption.